Creating an AWS Security Group
To allow communication between Dremio and other resources in your Amazon Virtual Private Cloud (Amazon VPC), a security group must be created.
To create a security group:
-
Go to the AWS Management Console and sign in with your credentials.
-
Navigate to Services > Networking & Content Delivery > VPC.
-
Select Security groups from the side navigation bar.
-
Click the Create security group button in the top right.
-
On the Create security group page, set the following:
a. Enter a Security group name and a Description to identify the policy (for example, dremio-SG and Outbound access to Dremio). These cannot be changed again once the group is created.
b. For VPC, select your created VPC.
c. Keep all other default settings.
-
Click the Create security group button.
Editing Inbound and Outbound Rules for the Security Group
Inbound Rules
You need to edit the inbound rules to allow communication between Dremio Cloud engine nodes. All engine nodes are within your AWS VPC. There is no inbound communication needed from Dremio into your VPC.
To edit inbound rules:
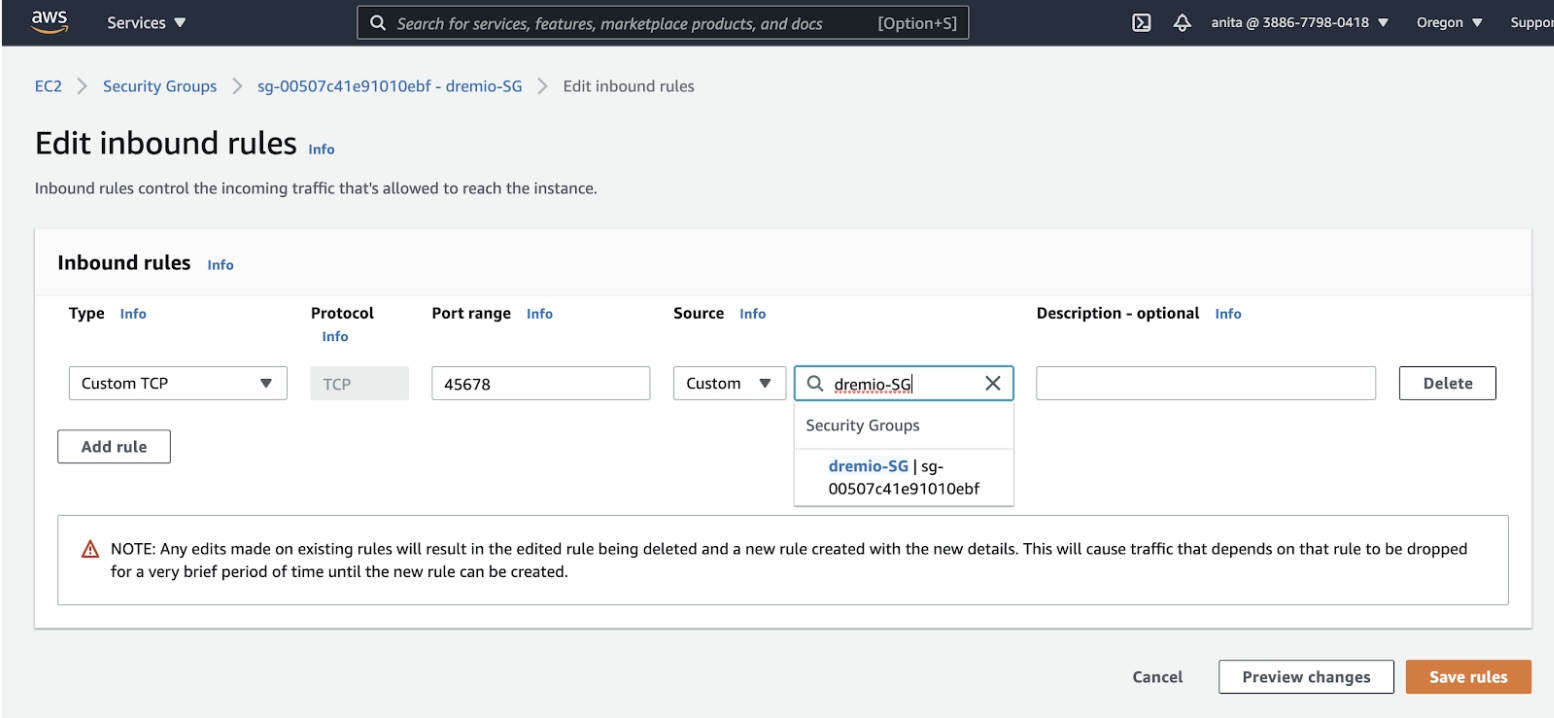
- Find the security group you created in the previous step (for example dremio-SG) and select the Edit inbound rules button in the bottom left.
- On the Edit inbound rules page, click the Add rule button and set the following:
a. For Type, select Custom TCP.
b. For Port range, enter 45678.
c. For Source, select Custom. If your security group (for example dremio-SG) is not pre-populated, select it from the dropdown.
If you're setting up a PrivateLink configuration, complete steps 3 and on. Otherwise, skip to step 7.
- Click Add rule again.
- For Type, select Custom TCP or HTTPS.
- For Port range, enter 443.
- Select the same Source as the first rule.
- Click Save rules.
Outbound Rules
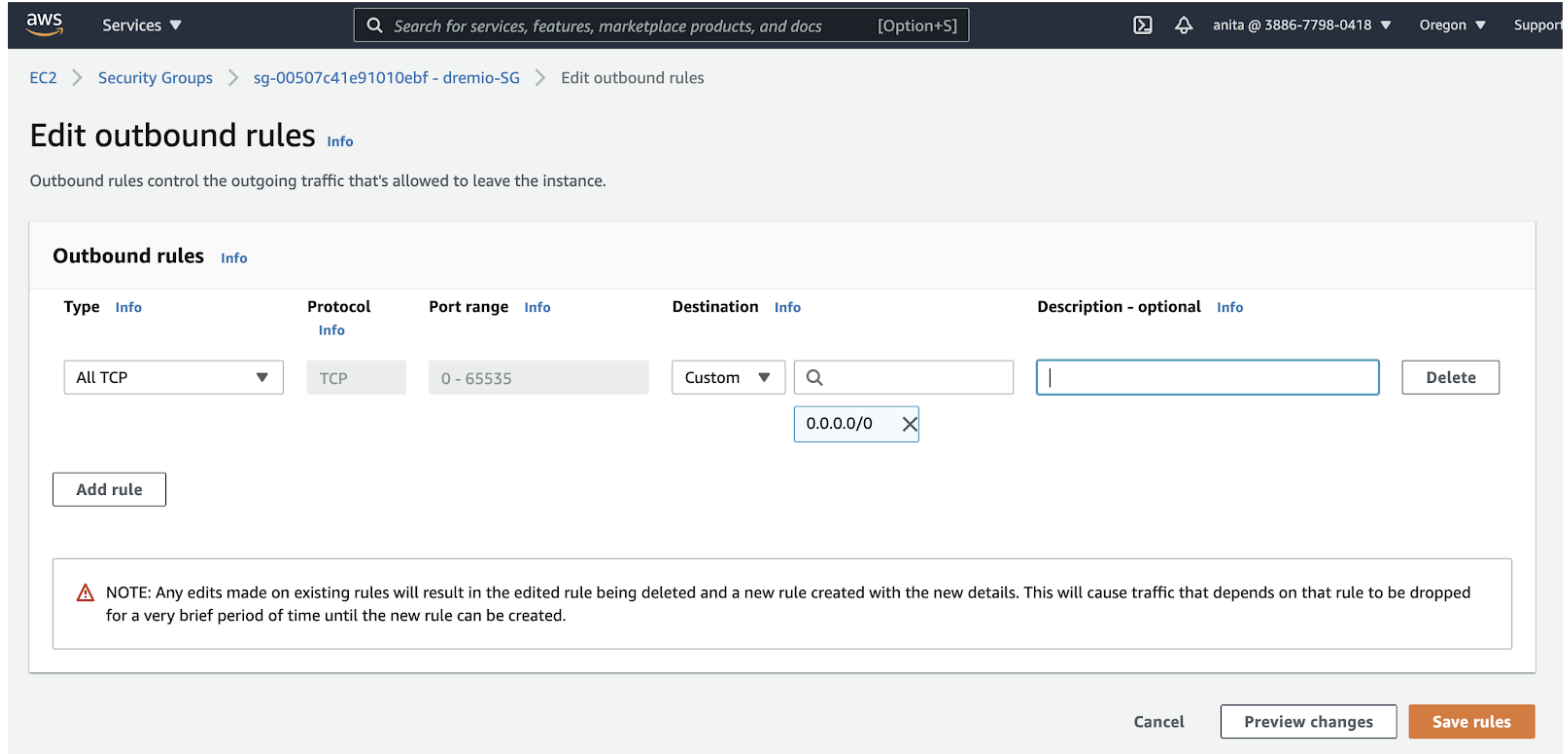
Edit outbound rules to allow Dremio Cloud engines in your VPC outbound access to connect to S3 and other sources.
To edit outbound rules:
- Find the security group you created (for example dremio-SG) and click the Outbound rules tab.
- Click the Edit outbound rules button in the bottom left.
- On the Edit outbound rules page, click the Add rule button and set the following: a. For Type, select All TCP. b. For the Destination, select Custom and then 0.0.0.0/0 from the dropdown.
- Click Save rules.
Additional Information
- Inbound rule: Rules for a security group that authorize or revoke access to receiving/inbound traffic (ingress).
- Outbound rule: Rules for a security group that authorize or revoke access to sent/outbound traffic (egress).
- Security group: Virtual firewalls for a VPC that control both inbound and outbound traffic (via rules).
- VPC: Also known as a virtual private cloud, these act as virtual networks based solely off your AWS account and are completely isolated from any other AWS Cloud virtual networks.